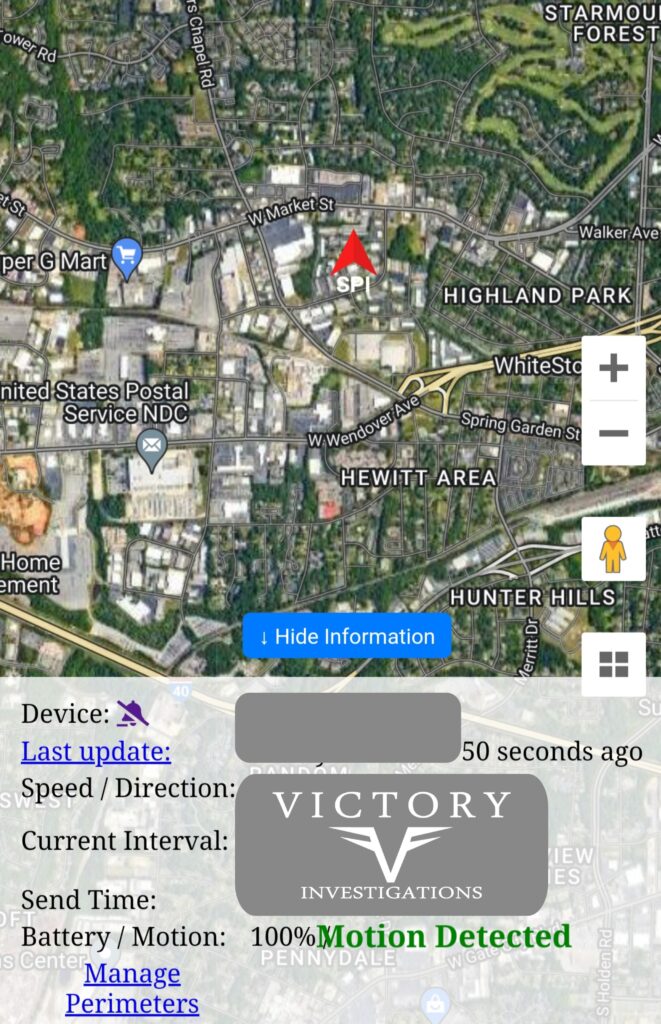
In Greensboro, North Carolina, Victory Investigations has earned a strong reputation as a go-to source for recovering lost digital data. As a licensed North Carolina Private Investigation Firm and Certified Digital Forensics Examiners, Victory Investigations is uniquely equipped to recover sensitive and high-stakes digital assets with professionalism and precision.
In the early days of Bitcoin and other cryptocurrencies, users were often casual hobbyists, storing digital wallets, seed phrases, and private keys in simple text files on their computers. Few anticipated the explosive rise in value these assets would see over the next decade. Unfortunately, this has led to a modern digital gold rush—not just in trading, but in recovering lost or inaccessible cryptocurrency assets that remain stranded on old or damaged hard drives.
From forgotten seed phrases to corrupted HDDs and accidental deletions, billions of dollars in Bitcoin (BTC), Ethereum (ETH), and other altcoins are believed to be lost. Thankfully, digital forensic experts can help recover these assets, using advanced techniques and forensic-grade software to search deep within digital storage.
How Cryptocurrency Gets Lost?
Unlike traditional banking systems, cryptocurrency ownership is determined solely by possession of the private key. Lose the private key, and the funds are lost—forever. The blockchain has no customer support line. This stark reality is the root of many cases where people have lost access to:
- Wallets with tens or hundreds of Bitcoins.
- Ethereum-based smart contracts.
- Altcoin holdings stored in non-custodial wallets.
Common Causes of Crypto Loss:
- Accidental Deletion: Text files with seed phrases, wallet.dat files, or password managers are inadvertently deleted.
- Damaged Hard Drives: Physical failure due to age, power surges, or water/fire damage.
- Formatting or OS Reinstall: A fresh installation of Windows or Linux erases partitions containing wallet files.
- Misplaced Devices: USB drives, external hard drives, or old laptops that once stored wallets go missing.
- Forgotten Credentials: Encrypted wallets or password managers locked behind forgotten master passwords.
Many assume these assets are unrecoverable. But that’s not always the case.
Meet the Experts: Victory Investigations of Greensboro
Victory Investigations, located in Greensboro, NC, is a licensed private investigation agency with specialization in digital forensics, OSINT investigations, and data recovery. The firm is fully certified to conduct forensic examinations of electronic devices—whether computers, mobile phones, servers, or storage drives.
Credentials and Capabilities:
- Licensed in North Carolina as a Private Investigation firm.
- Certified in Digital Forensics and Technical Surveillance Countermeasures.
- Members of international associations including ASDFeD and HTCIA.
- Experts in chain-of-custody handling for potential civil or criminal litigation.
- Equipped with state-of-the-art forensic tools.
Tools of the Trade
Victory Investigations uses a range of elite forensic platforms, including:
- Cellebrite UFED: Industry-standard for mobile device forensics.
- Magnet AXIOM: Advanced forensic suite for examining file systems, carved data, browser histories, and artifacts.
- Detego: Rapid triage and analysis tool used by law enforcement.
- Belkasoft Evidence Center: Great for encrypted and partially corrupted data.
- Oxygen Forensics: Ideal for mobile and app data recovery.
- FTK, Paladin Sumuri: Used for raw disk imaging, carving, and metadata analysis.
These tools allow forensic examiners to reconstruct deleted partitions, locate remnants of wallet files, identify web-based crypto activity, and even find browser autocomplete data containing valuable hints.
What is a Digital Forensic Examination?
When someone suspects they’ve lost cryptocurrency stored on a hard drive or device, Victory Investigations follows a careful, methodical process to ensure no evidence is destroyed and all recovery options are pursued.
1. Forensic Imaging
The device is write-blocked and imaged—meaning a bit-by-bit copy of the drive is created. This ensures that the original data is preserved. Tools like FTK Imager or AXIOM Process are used to create forensic copies.


2. Artifact Search
The next step is parsing the image for crypto-related artifacts:
- wallet.dat files (used by Bitcoin Core)
- Mnemonic phrases (seed phrases) matching BIP39 word lists
- .ldb LevelDB storage (used by Ethereum geth)
- Files from applications like Electrum, Exodus, MetaMask
- Password hints in Notepad or browser auto-fill
For instance, searching a drive for 12 or 24-word BIP39 phrases can yield crucial results.
3. Deleted Data Carving
Even if the files were deleted, many remnants can be recovered from unallocated space using data carving. Victory uses Detego and AXIOM to:
- Recover deleted .dat files.
- Carve out browser histories and autofill data.
- Locate encrypted containers that may house crypto credentials.

4. Password Recovery and Brute Force
If the wallet or file is encrypted, Victory employs GPU-accelerated password cracking tools like Hashcat or Elcomsoft, sometimes in combination with clues recovered from:
- Old emails or notes.
- Browser autofill.
- File metadata and timestamps.
This stage may take days or weeks depending on the encryption.
Case Example: $75,000 in Bitcoin Recovered
A recent client of Victory Investigations approached the firm after finding an old laptop during a move. It hadn’t been turned on since 2014. The client vaguely remembered using Bitcoin Core but had long lost the password.
Victory’s forensic team created an image of the laptop’s drive and discovered a deleted wallet.dat file in unallocated space. After carving it out and confirming the wallet held over 1.5 BTC, the team then recovered browser-stored password fragments that helped piece together the correct password to decrypt the wallet.
Total recovery: ~$75,000 in Bitcoin (at current market value).
Best Practices to Avoid Losing Crypto Assets
While recovery is possible, prevention is the best strategy. For those storing digital currencies:
- Use hardware wallets (Ledger, Trezor) and store recovery phrases offline.
- Avoid storing seed phrases in plain text on devices.
- Document passwords and key details and store them in a secure location.
Keep devices clean and malware-free using endpoint security.
Why Choose Victory Investigations?
Crypto recovery isn’t just about tools—it’s about experience, legal compliance, and forensic precision. Victory Investigations provides:
- Legally defensible digital imaging and reports.
- Confidential consultations and in-lab recovery.
- 14 years of experience in digital forensics and cyber investigations.
- Affordable services with full transparency.
They serve not only North Carolina but accept nationwide and international clients seeking crypto asset recovery.
Final Thoughts
As the cryptocurrency space matures, the importance of secure storage grows—but so does the need for experts who can help recover lost or inaccessible assets. If you or someone you know suspects they have old crypto stored on a device, don’t throw it away—have it examined by professionals.
Contact Victory Investigations Today!
1-888-482-6273 OR (336) 298-2034